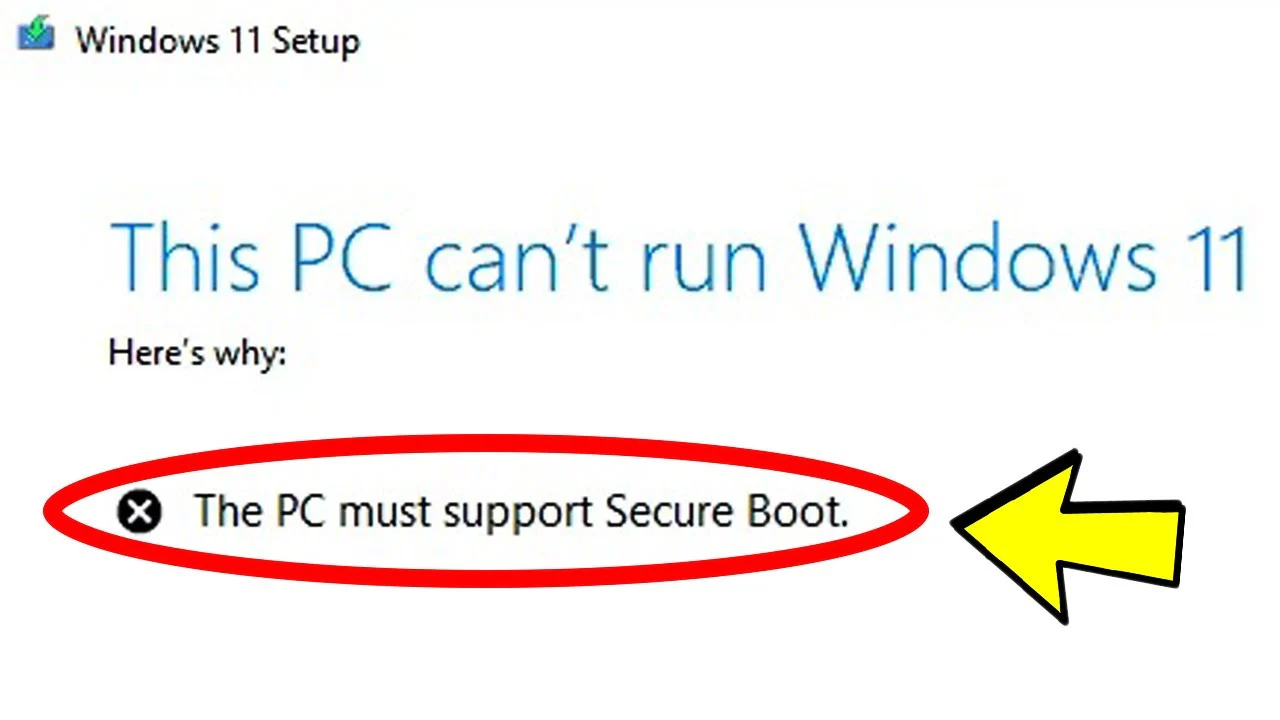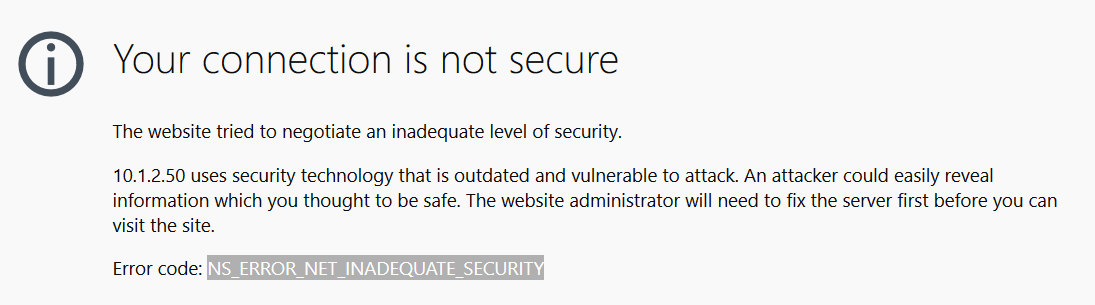
If you’ve recently upgraded an IIS web server to Windows Server 2016, you may come across a NS_ERROR_NET_INADEQUATE_SECURITY error in Firefox or an ERR_SPDY_INADEQUATE_TRANSPORT_SECURITY error in Google Chrome. There are a few reasons for this and the main one is that IIS in Windows Server 2016 turns on HTTP/2 by default and only falls back to the older HTTP/1.1 if the browser doesn’t support HTTP/2. While HTTP/2 is generally a good thing and most recent browser support it, it also has stricter requirements than HTTP/1.1 and the issue with these browser errors is that the Windows Server 2016 is trying to establish an HTTP/2 session with the browser but the server is configured with some weaker SSL Ciphers which aren’t supported by HTTP/2.
At the server level, there are a few options you have to resolve this issue. First, you can disable the weaker cipher suites, which is recommended for security purposes, and leave HTTP/2 enabled. The second option is to disable HTTP/2 in IIS and only use the older HTTP/1.1 standard. We’ll walk you through both options.
Disable Weak Cipher Suites
The easiest way to toggle cipher suites and SSL protocols is by using a utility called IISCrypto which you can download here. When you open IISCrypto, you can use the Best Practices button to automatically disable insecure protocols and weaker cipher suites. You’ll need to reboot to make the changes take effect. If you’re more advanced, you can fine tune these protocols and cipher suites manually using IISCrypto as well.
Disable HTTP/2 in IIS on Windows Server 2016
If you decide to disable HTTP/2 in IIS on Windows Server 2016 and only use HTTP/1.1, you can do so by adding two DWORD registry keys. You can copy the text in the box below into an empty Notepad file and save it as a .reg file. Then double-click the file to import the registry keys and reboot.
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\HTTP\Parameters]
“EnableHttp2Tls”=dword:00000000
“EnableHttp2Cleartext”=dword:00000000
If you decide to enable HTTP/2 at a later time, you can either delete the two registry keys or change their values to 1.
How to Disable HTTP/2 in Firefox
If you’re trying to browse to a website and you’re getting the error NS_ERROR_NET_INADEQUATE_SECURITY in Firefox and you’re not an administrator of the server, you can disable HTTP/2 in Firefox.
- Open Firefox and type about:config in the address bar
- Click on I Accept The Risk
- Search for network.http.spdy.enabled.http2
- Change the value to False
- Restart your browser