A few months ago, I wrote an article on how to configure IIS for SSL/TLS protocol cipher best practices. To test your configuration, you can use a handy tool called NMap (nmap.org) or the ZenMap GUI.
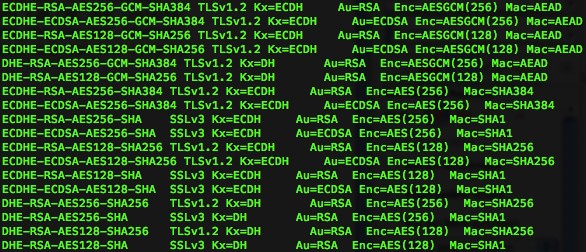
Included in NMap is a script called ssl-enum-ciphers, which will let you scan a target and list all SSL protocols and ciphers that are available on that server. You can also narrow it down by specifying a port number with the -p option.
Using NMap, the script would look something like nmap --script ssl-enum-ciphers [fusion_builder_container hundred_percent="yes" overflow="visible"][fusion_builder_row][fusion_builder_column type="1_1" background_position="left top" background_color="" border_size="" border_color="" border_style="solid" spacing="yes" background_image="" background_repeat="no-repeat" padding="" margin_top="0px" margin_bottom="0px" class="" id="" animation_type="" animation_speed="0.3" animation_direction="left" hide_on_mobile="no" center_content="no" min_height="none"][target] where [target] is the IP or hostname of the server you want to scan. You can also specify the port by adding -p to the command: nmap -p [port] --script ssl-enum-ciphers [target] where [port] is the port number you want to scan. If you do not specify a port number, it will scan all ports on the server and return the results for each port that is configured to use SSL.
This tool comes in handy if you’re doing a vulnerability scan and you need to make some changes to a server and you want to test those changes. This will allow you to perform a quick scan without needing to do a complete vulnerability scan.
You can read more about this NMap script here: https://nmap.org/nsedoc/scripts/ssl-enum-ciphers.html[/fusion_builder_column][/fusion_builder_row][/fusion_builder_container]




Where is the script?
It is included in NMap, you just need to run the command as described in the article.
would recommend using the -Pn flag on this as well.